![PDF] Automated Detection of Side Channels in Cryptographic Protocols: DROWN the ROBOTs! | Semantic Scholar PDF] Automated Detection of Side Channels in Cryptographic Protocols: DROWN the ROBOTs! | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/ecbfad1458c7ade36ace5544067bdcdceec0b09a/12-Figure6-1.png)
PDF] Automated Detection of Side Channels in Cryptographic Protocols: DROWN the ROBOTs! | Semantic Scholar
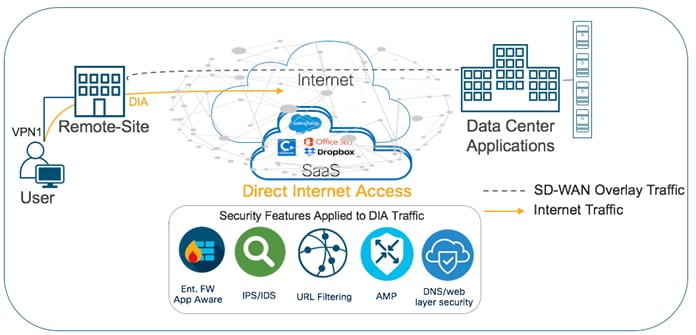
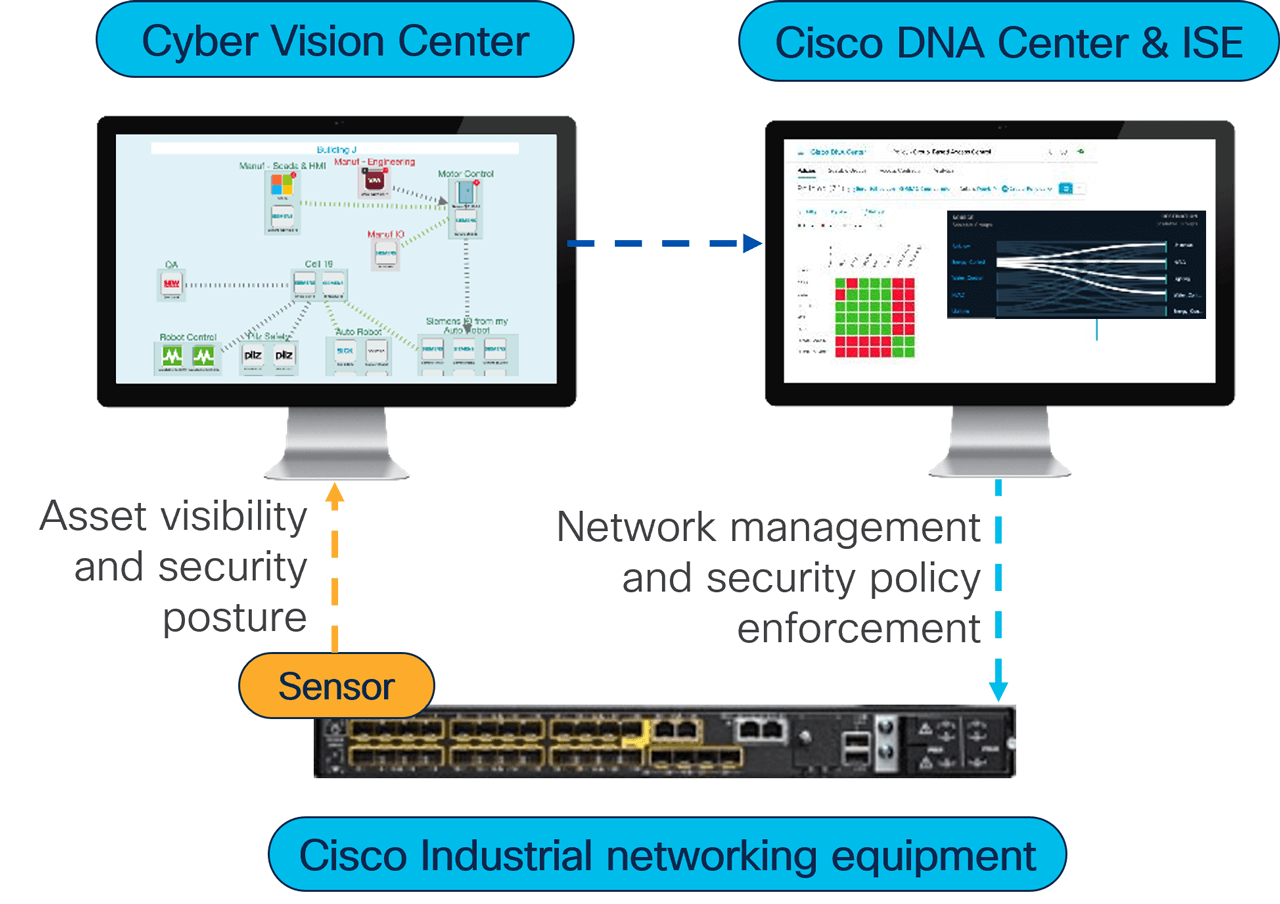
Deploying Identity and Mobility Services within a Converged Plantwide Ethernet Architecture Design and Implementation Guide

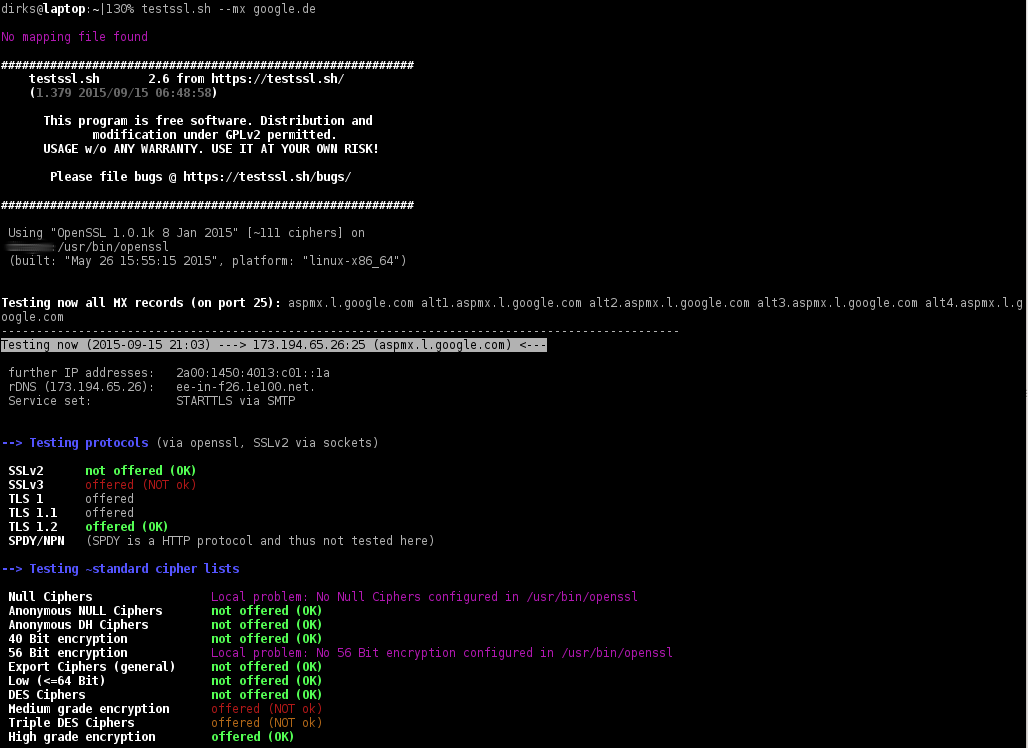
CTHSEC-1001-The Future of Transport Layer Security | PDF | Transport Layer Security | Computer Network Security

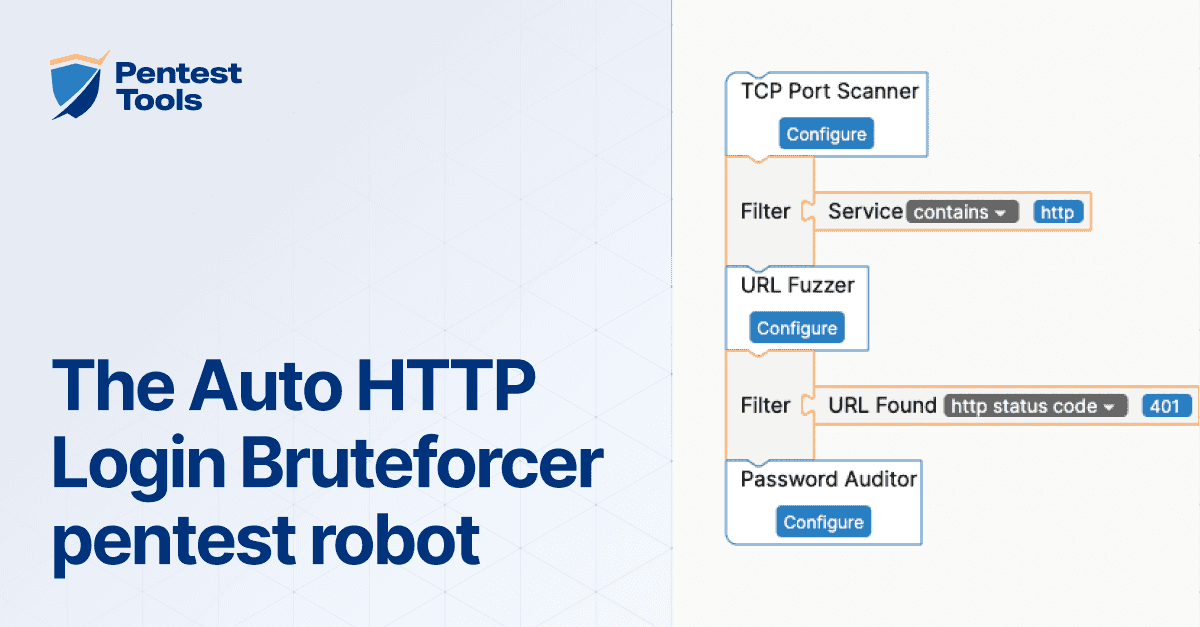
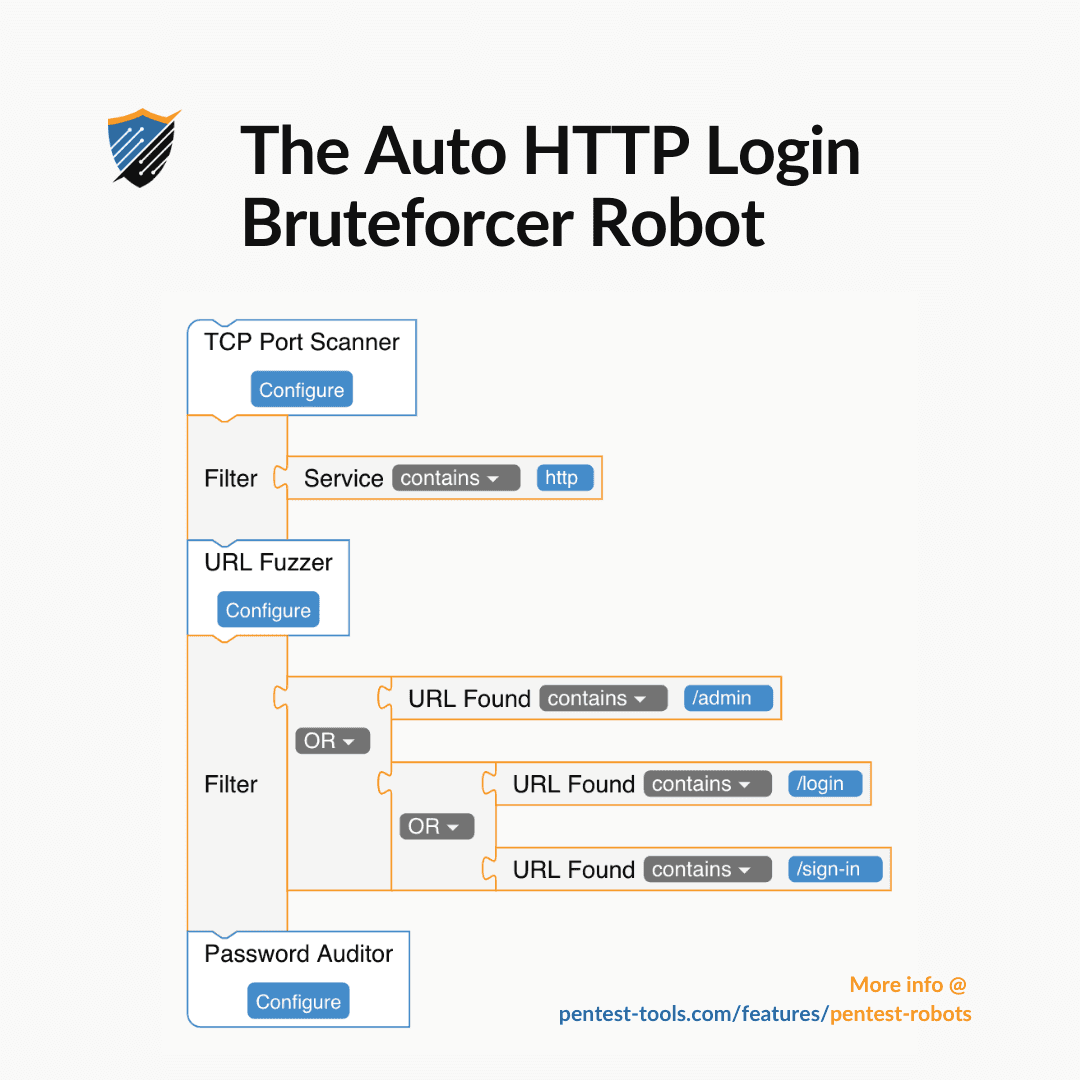
Vulners – Google for hacker. How the best vulnerability search engine works and how to use it | Alexander V. Leonov